Most healthcare data loses its value long before it loses its sensitivity label. The industry does not have a protection problem; it has a valuation problem. Healthcare cybersecurity still operates on the assumption that all patient data is equally valuable and dangerous, driving unreasonable budgets, fragmented controls, and a security posture that tries to protect everything yet prioritizes nothing. This is why hospitals often encrypt decades-old records with the same rigor as real-time ICU telemetry, even though the risk and impact are fundamentally different.
The reality is uncomfortable yet clear. Stolen claims data or ancient prescriptions have rarely caused direct patient harm. The deeper issue is not insufficient controls, but a lack of intent. Healthcare CISOs must move beyond securing everything to securing what truly matters: data that is critical for care and patient trust and data that can be safely retired or deleted.
The idea of “securing everything” comes from a historically driven mindset, i.e., the system will always reward volume over value. HIPAA’s broad definition of protected health information has long encouraged long-term data retention and uniform security controls. Also, widely repeated claims about the resale value of medical records have reinforced fear-driven protection strategies. In reality, most modern attacks on healthcare are not about monetizing data at scale. They’re about leverage. Hospitals are targeted because disrupting care creates immediate pressure through operational downtime, regulatory exposure, and reputational risk.
If the threat has shifted from data theft to operational disruption, security strategies must shift as well. In practice, this means moving away from blanket controls and toward deliberate lifecycle-based protection. A three-year-old administrative record won’t warrant the same real-time security investment as active patient monitoring systems. By tiering protection based on actual threat vectors and business impact, healthcare organizations can reduce their attack surface while freeing resources and data for innovation.
HFS Research believes that the real shift healthcare security leaders must make is from system-based protection to purpose-based protection. Data does not have a single, permanent value simply because it sits within a hospital or payer. Its risk profile changes based on what it is, why it exists, and how long it is needed.
To help security leaders move from broad protection to deliberate prioritization, we have outlined three practical data archetypes (see Exhibit 1). These archetypes are not theoretical. They are designed to help CISOs align controls, budgets, and accountability with real-world risk.
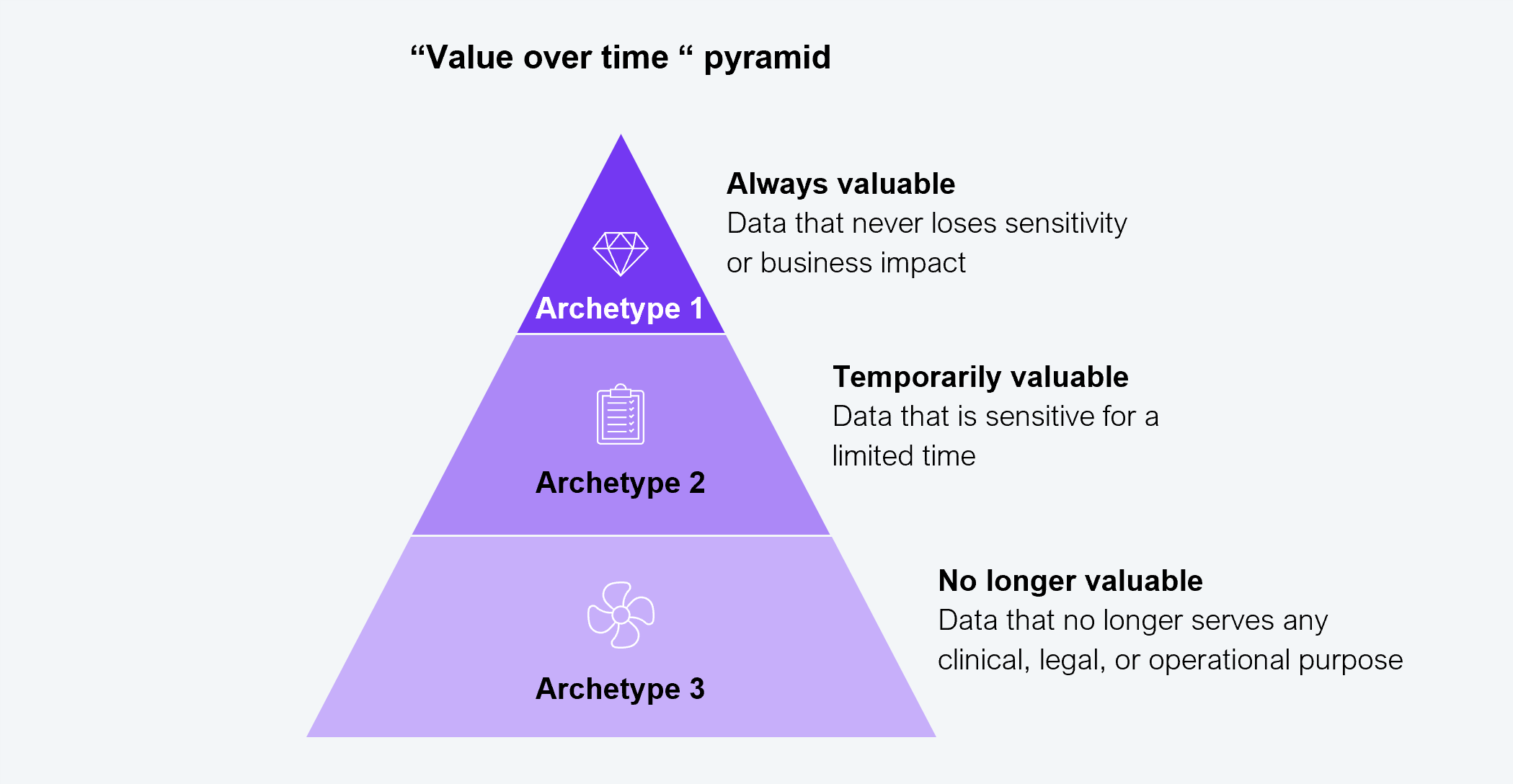
Source: HFS Research, 2026
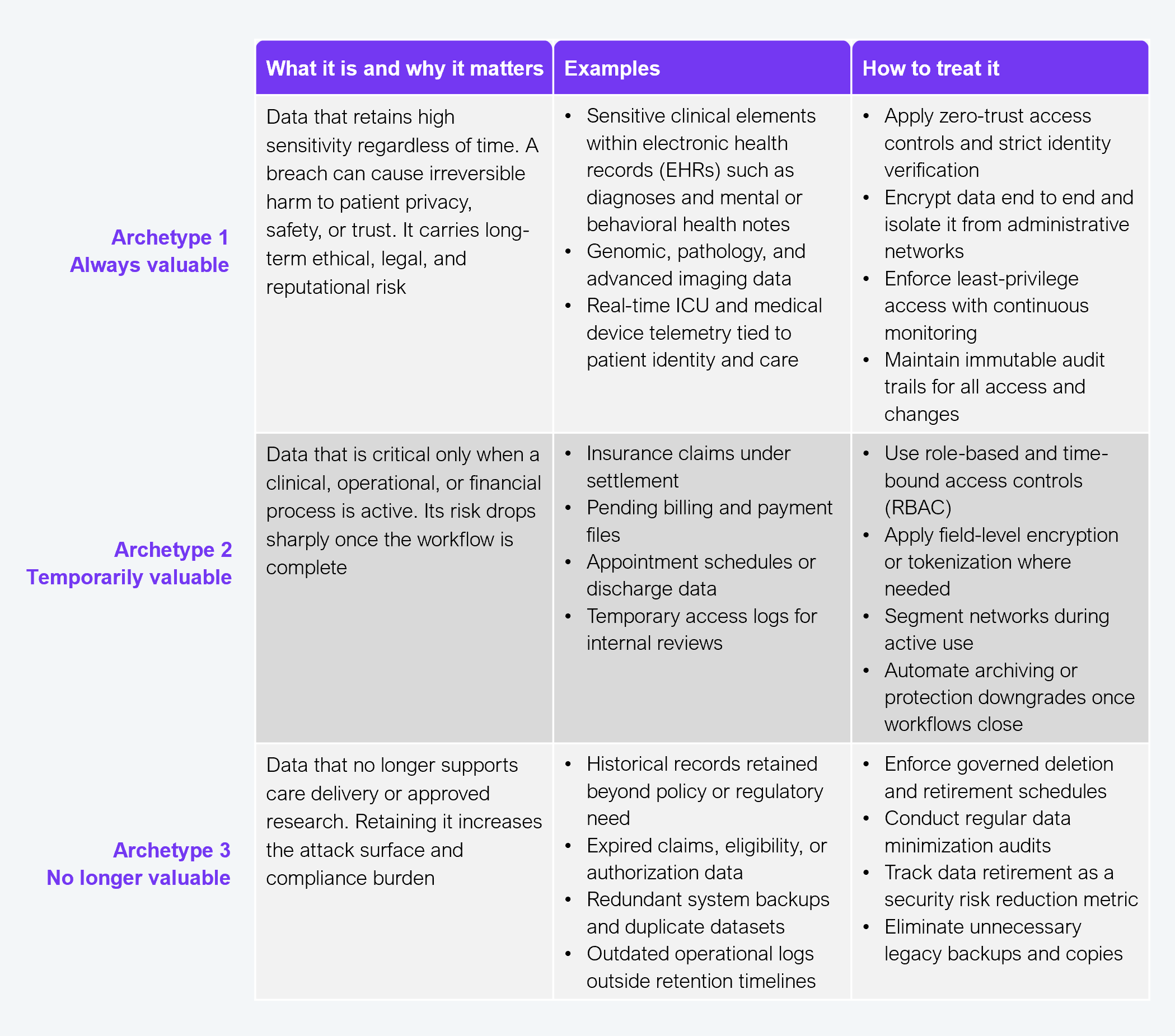
Source: HFS Research, 2026
This model is not about reducing protection but about proving control. By classifying data based on purpose and lifespan, healthcare organizations can deploy advanced defenses where they matter most, reduce unnecessary exposure elsewhere, and create clearer accountability across the data lifecycle.
Those leading in this space do not need more tools or controls. They need focus because the current risk isn’t weak technology; it is unclear priorities. Checking regulatory boxes designed for decades-old threats will not safeguard against today’s ransomware and operational disruption attacks.
The velocity gap between technology evolution and regulatory updates means that adaptive security models, not just audit readiness, are what actually protect patients and operations. The cyber-resilient healthcare leaders will secure what matters while enabling innovation, not locking down everything in the name of compliance.
Register now for immediate access of HFS' research, data and forward looking trends.
Get StartedIf you don't have an account, Register here |
Register now for immediate access of HFS' research, data and forward looking trends.
Get Started