This HFS Point of View is for chief procurement officers mapping digital sovereignty exposure across vendor contracts before the next renewal cycle locks in three to five more years of risk.
Digital sovereignty has stopped being a regulatory abstraction. It is arriving in enterprise vendor portfolios as contract clauses CPOs did not write. Sovereign buyers (governments, defense ministries, regulated institutions like the ICC leaving Microsoft, NATO air-gapping its cloud, France moving 2.5 million civil servants off US platforms) are forcing vendors to rebuild for the strictest customer, and that standard then cascades contractually into every supply chain that touches the same vendors, including yours.
Sovereignty now belongs on the CPO’s desk as a supply chain risk, and the window to shape it is the next renewal cycle: every contract signed on the old assumptions locks in three to five more years of exposure, and the early-exit rights enterprises hold today under the EU Data Act do not survive it. This piece gives CPOs a working definition, the four pillars to measure exposure against, and five moves to make before the next renewal.
Your vendor stack was built on the quiet bet that borders between allied democracies did not really apply to data, US cloud providers were neutral global infrastructure, and the rules-based order would just keep going. Nobody wrote it down, and every contract assumed it. Because the bet kept paying off, enterprises missed the three successive eras of sovereignty risk in Exhibit 1. Each warning signal looked like noise until the next one arrived.
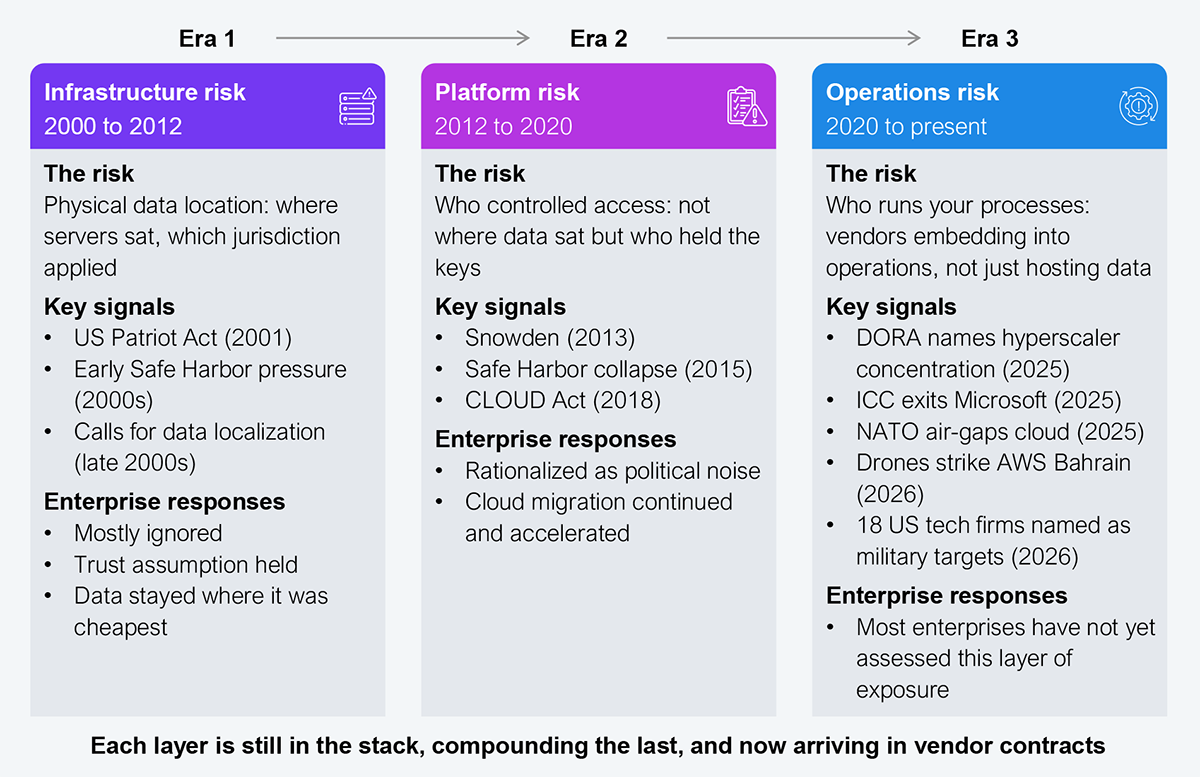
Source: HFS Research, 2026
Era 3 breaks the pattern. The earlier signals could be rationalized as political noise and waited out; this one arrives inside vendor contracts, where it cannot. National interests are back inside vendor contracts, jurisdictions are competing for control of data, and regulators are starting to enforce what governments have been signaling for years. Every unresolved exposure from the first two eras is still sitting in the stack, now compounded by the third.
What most private-sector leaders miss is that the sovereign-buyer mandate does not stay contained to governments and defense. When sovereign buyers mandate hardened architectures, vendors cannot sustain multiple parallel stacks in perpetuity. They rebuild for the strictest customer, and that standard then cascades contractually through every supply chain that touches them. By the time sovereignty reaches the private sector, it arrives as a clause, not a choice.
Most enterprises cannot define sovereignty for their own operations, and they cannot manage what they have not defined. HFS defines it as an organization’s ability to maintain meaningful control over its digital assets, systems, and dependencies, such that if trust breaks anywhere, the organization can still operate and govern itself.
In practice, that control rests on four pillars: where your data can be reached (jurisdictional control), whether you can actually leave (operational portability), who owns the question internally (governance ownership), and whether you can keep running when the infrastructure underneath you cannot (infrastructure resilience). Most enterprises have a gap on at least one, and many have gaps on all four (see Exhibit 2).
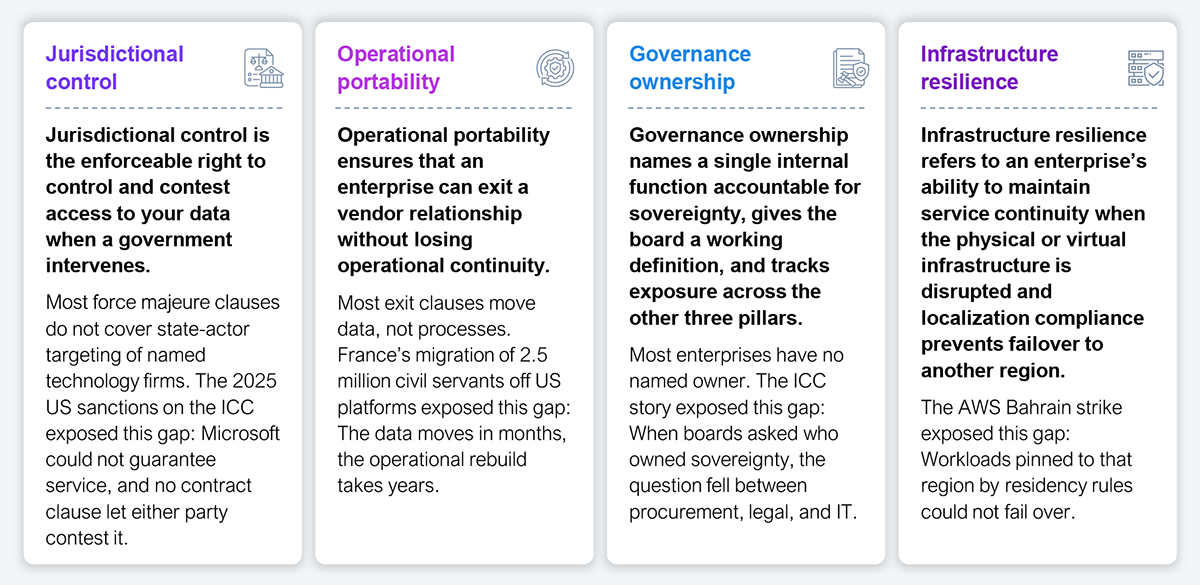
Source: HFS Research, 2026
You do not need a complete transformation program to start. You need a few moves you can make inside contract cycles you are already running, and they go in roughly this order: own it, see it, use the rights you already have, enforce the standard going forward, and stress-test the edges (see Exhibit 3).
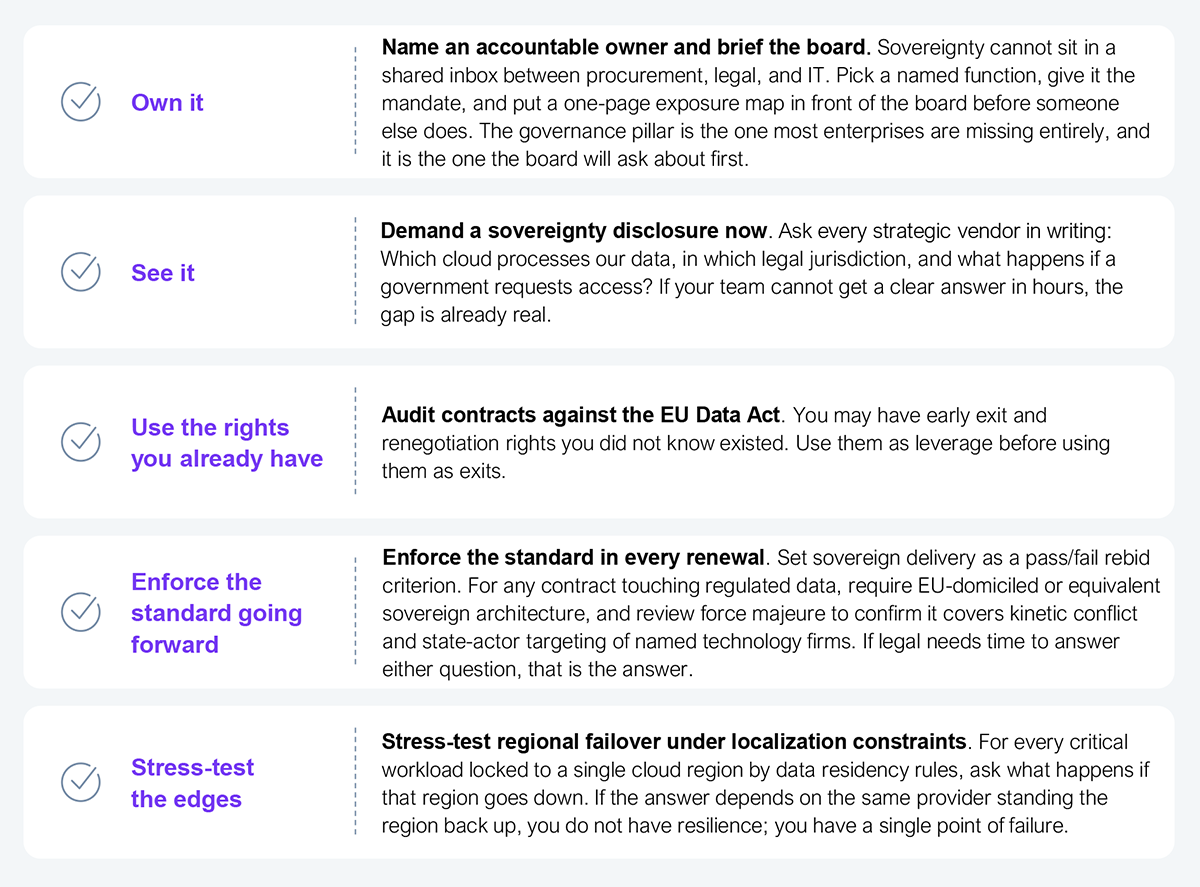
Source: HFS Research, 2026
Sovereignty is not a procurement risk. It is supply chain risk that lands squarely on the CPO’s desk. Your job is to turn it into enforceable control, credible exit paths, and board-level visibility. Lead it or be led by it.
Register now for immediate access of HFS' research, data and forward looking trends.
Get StartedIf you don't have an account, Register here |
With the exception of our Horizons reports, most of our research is available for free on our website. Sign up for a free account and start realizing the power of insights now.
Our premium subscription gives enterprise clients access to our complete library of proprietary research, direct access to our industry analysts, and other benefits.
Contact us at [email protected] for more information on premium access.
If you are looking for help getting in touch with someone from HFS, please click the chat button to the bottom right of your screen to start a conversation with a member of our team.